Windows 10 VPN before login for domain users
How to create a VPN connection before logging in to Windows 10
I just thought I’d post a quick help guide for those struggling with remote sites that have no site-to-site VPN. For whatever reason the site has no VPN, you can get new users logged into a domain by connecting to the VPN before log on.
The situation
I’ve been looking after a site that has remote users and due to the fact the remote office is shared with other companies, it is not possible to set up a site-to-site VPN.
In the past, we have set up new computers at the head office, got the user to log-in and then ship the PC to site. Once on the remote site, they can log in and connect to the VPN to get access to the network shares.
This is becoming more difficult as new users are starting at the remote location and need to log in for the first time from there.
The solution
It’s not obvious how to set up a VPN before the windows login process but I have found the answer.
You need to run the following command from an elevated Powershell window (right-click, – ‘Run as Administrator). You will need to substitute VPN_NAME with a name of your choice and VPN_SERVER_ADDRESS with the IP address or domain address of your VPN server:
Add-VpnConnection -Name VPN_NAME -ServerAddress VPN_SERVER_ADDRESS -AllUserConnection $true -SplitTunneling $true -AuthenticationMethod MSChapv2 -TunnelType Automatic -EncryptionLevel Required -PassThru
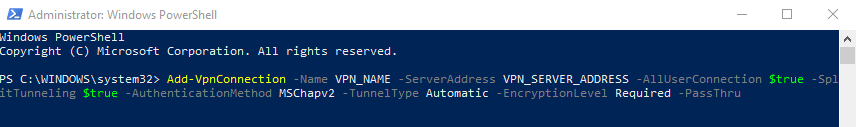
If you want to use a specific type of VPN you can change the -TunnelType
eg. -TunnelType “PPTP” or -TunnelType “L2TP” -L2TPpsk “PassKey”
The result
Once you’ve run the add VPN script above, log off the PC. At the login screen, you will see a new network icon in the bottom right of the screen.
Click on that, and it will prompt for your VPN username and password.
I’m using Microsoft Routing and Remote Access for VPN access, which is linked to Active Directory.
This means the user just has to put in their Windows username and password. This then connects the VPN and they get logged into Windows.
Additional Notes:
Please also note you might need to add a Registry key for L2TP if you have NAT on your routers.
Under HKLM\SYSTEM\CurrentControlSet\Services\PolicyAgent
Add a DWORD AssumeUDPEncapsulationContextOnSendRule with a value of 2 if both devices are behind NAT firewalls or a value of 1 if one end is behind a NAT Firewall.
If you don’t want to go down the VPN route you can always try some remote access software such as LogMeIn* or check out my IT Tools page for more options
Let me know if this helps in the comment section below, or check out my other support posts here
Another way of supporting me would be to buy me a coffee by clicking below
 Buy me a coffee
Buy me a coffee
Thanks
Ian
*Disclaimer – Links with a * are affiliate links where I may get paid or recognition but it won’t cost you any more.
26 Comments
Rene Castro
If you found your way here, you’re using Windows 11, and Windows Built-in VPN, this might work for you.
Summary:
You need to copy
C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\PBK
to
C:\ProgramData\Microsoft\Network\Connections\PBK
Thought I’d start with the summary for those who just want the red meat.
Here’s what I did:
I created a local admin user and setup a L2TP VPN connector with the Winows Built-In VPN software to an Edgerouter Lite. This works and I could ping my distant end devices using FQDN, for example server.****.local. I Then joined the domain and after reboot, logged back in as local admin, started VPN and added the domain user. Next was to log in as the domain user and setup a VPN connector. Using the same or differet VPN login credentials it fails showing error message: The system could not find the phone book entry for this connection.
The solution: Once you join the domain it seems that Windows, in it’s infinite wisdom, changes the location of where PBK files lay thus the VPN created by domain user cannot find the PBK files. As the domain user, remove the VPN connector you’ve created. Next Log in as the local admin, and find the PBK folder, mine was located at
C:\Users\admin\AppData\Roaming\Microsoft\Network\Connections\ Next I copied the PBK directory into following location,
C:\Users\\AppData\Roaming\Microsoft\Network\Connections\ as there was none. Be warned this DID NOT work because at this time I did not know of the correct location PBK should be. But it was a good place to stash the PBK folder which contanted the PBK files like rasphone.pbk. So store the PBK folder in a higher level folder accessible by all users. Which is best as there may have been ownership issues I bypassed by coping files using the local admin account.
The real location you want to copy the PBK folder to is C:\ProgramData\Microsoft\Network\Connections\
Log in as the domain user, Then copy the PBK folder from either the higher level directory you used or if you did what I did from the \AppData location I used originally. As we all know, domain user will have access to the other directories I’ve listed but possibly not the admin\AppData directory.
Once the copy is complete, you should see the VPN connector is now list in the VPN selection and it should work. That’s my 2 cents. I hope you find this helpful. Will this work in Windows 10? I don’t know. I tried this with a hope and a prayer and got lucky.
Silviu
Hi Jon,
The connection was succesfull created. I have the vpn icon on login page but cannot login because I get the error “User or password incorrect”. If I log into windows and start the connection from there the credentials works. Do you have any ideea what is the problem?
Thank you
Jon
Hello,
I have executed the command and a new VPN is added but after logoff I don’t see the possibility of connecting to the VPN before logging in.
The icons in the corner do not show the VPN.
My windows version is 21h1.
Regards
Ian
Hi Jon,
I haven’t tested with that version yet. If I get chance I’ll post an update.
Thanks for reading
Ian
Jon
Hello,
I have already solved. I can see the VPNs before the logon.
Of course, I have two laptops and I can only see them in the one that belongs to a domain.
Both version of WIN10 21H1.
Greetings.
Ian Salgado
Hi,
quick questions
which part of the command forces the vpn connection to come up ?
Add-VpnConnection -Name VPN_NAME -ServerAddress VPN_SERVER_ADDRESS -AllUserConnection $true -SplitTunneling $true -AuthenticationMethod MSChapv2 -TunnelType Automatic -EncryptionLevel Required -PassThru
I’m assuming is “-PasssThru”
cheers
Ian
Hi Ian,
This does not connect the VPN, just adds a connection that you can connect to before logging in.
-Passthru outputs the connection details to the powershell screen so you can see the settings applied.
Thanks
Ian
John
When you enter your AD credentials after selecting your VPN address does it automattically pasthrough to windows or are you foreced to login a second time using the same creds?
Ian
Hi John,
It automatically logs you in, as long as you’re using Microsoft RRAS for the VPN.
Regards
Ian
Garth
Hey Ian. Thanks alot for the Powershell script. I am having no joy. Script executes fine, and DOES create the PPTP VPN entry which works when I launch it through GUI and or command line rasdial [entry].
I expect I would see the two comupter icon in the lower right (I’ve seen them before), but it’s just not being added.
Have you tried with the latest Windows? Just curious.
Thank you again for sharing!
Garth
Ian
Hi Garth,
Thanks for your comment. I have not had to use this script lately so can’t say definitely if it will or will not work on the latest Windows 10 release.
I can’t see why it wouldn’t work though.
If I get a chance I’ll try it out and report back.
Ian
Manu
Hi,
I follow all steps and I created vpn access, but when I try to log in, I got the message “we can’t access to your session because domain isn’t available” .
My VPN connection works, even when I type my credentials I achieve to connect but when I got error message it clearly disconnect from router.
any idea?
Thanks you.
Ian
Hi Manu,
This sounds like a DNS issue from the message you get. If you log in and then connect the VPN manually can you ping the domain controller?
Also, you mention a router, this works when you are using Microsoft Windows Server RRAS for the VPN rather than a VPN to a router.
Hope this helps
Ian
Brian Zellinger
Thanks for the tutorial. Do you know if there is a way to auto log the user in using this method?
Ian
Hi Brian,
Thanks for your comment.
I don’t think there should be a way to do this.
This is too much of a security risk, to have the computer automatically log into a (business) network without a password as a minimum.
I can’t think of a good reason to do this. If you would like to expand the scenario I may be able to help.
If a computer is lost/stolen the whole network is vulnerable.
Thanks
Ian
Paolo
Is there a way to add the additional network icon at login screen for existing VPN Connections? We use a IKEv2 certificate-based connection and the script provided about doesn’t work even if I want to create a second connection
Thank you!
Ian
Hi Paolo,
Thanks for leaving a question. You could try “Set-VpnConnection -Name EXISITING_VPN_NAME -AllUserConnection $true”, where EXISTING_VPN_NAME is your current VPN name. Please let me know how you get on.
Thanks
Ian
JohnD
I’m wondering if that suggestion for Paolo worked, as I have the exact same situation and would help to find out if this is possible. We need to change Domain on remote laptops, and need the VPN to be up and running prior to login. Thanks!
Ian
Hi John,
Unfortunately, I’ve not heard back from Paolo. If you do any testing and find a solution please post back to let us all know.
Thanks
Ian
Jay
Not Paolo, but I attempted this myself with Anyconnect VPN provider for Windows VPN client and receive the following:
Set-VpnConnection : The configuration cannot be applied to the global user VPN connection [vpn connection name] : The system could not find the phone book entry for this connection.
I recognize this is a bit different as I’m making use of the Anyconnect adapter found in the Microsoft Store, but hoping there’s a good way to make this work to allow mobile users to login using domain credentials over VPN.
Ian
Hi Jay,
I’m not sure how Anyconnect VPN works I’m afraid. The Set-VPNConnection modifies an entry in the rasphone.pbk.
If Anyconnect does not add an entry in the rasphone.pbk, then the command won’t work. (You can open the file with notepad to check).
The rasphone.pbk is found in C:\Users\username\AppData\Roaming\Microsoft\Network\Connections\Pbk for users VPN’s and as it’s per user, obviously only available after login.
The Global VPN rasphone.pbk is where the VPN is stored if it is available before login and can be found in C:\ProgramData\Microsoft\Network\Connections\Pbk.
I’m not sure if this will help you but hope it explains a bit more.
Ian
Roger Leemann
Hi
I came this far on my own, however the stumbling block for me ist that in our environment we use different credentials for VPN and domain login. I haven’t found a way to first connect the VPN and then log in with differnet credentials to the domain. Is there any?
Regards
Roger
Ian
Hi Roger,
Thanks for your visit to my web site. I have just tested this from a non-domain PC (Windows 10 Pro) to a Windows domain, and the VPN connected but gave an error it was unable to log on to the computer. I was able to go back and log into the PC with my Pin and the VPN was connected. However, I would not use this method for end-users unfortunately as it’s not a clean process. Sorry, I’m not sure of a better way.
Regards
Ian
Roger Leemann
Hi Ian
Just a short follow-up. Thanks for the suggestion. Unfortunately in our case this doesn’t seem to work. The only way I found, is to login as another (local) user, turn on the vpn and then switch user. Not enduser friendly as they normally don’t know another login but at least I could get them started that way with a little help from my side via TeamViewer or some other remote support tool.
Best regards
Roger
Salim Lohiya
Ian,
You are the MAN, what a simple yet elegant solution which has got me out of a hole
Thank you
Slim
Ian
Glad it helped you out Salim,
Ian